Mastering basic Mobile Device Management (MDM) operations is an essential skill set for administrators tasked with safeguarding an organization's mobile assets. Whether you're new to MDM administration or looking to reinforce your existing knowledge, this complete guide is designed to equip you with the foundational skills required to manage devices effectively.
This article is part of our guide "Mastering Mobile Device Management Operations: A Guide for Admins".
Device Enrollment
Overview of Device Enrollment Methods
Device enrollment serves as the critical foundation for any complete Mobile Device Management (MDM) strategy. Understanding the various methods available, each with its unique pros and cons, can significantly enhance the effectiveness of your MDM administration. Here are some of the most common methods:
Over-the-Air (OTA)
How it Works: Admins send an enrollment invitation via email or SMS, containing a secure link for the end-user to initiate the enrollment process.
-
Pros:
- Scalable for large deployments
- Minimal manual intervention required from the end-user
- Efficient for remote setups
-
Cons:
- Requires reliable internet connectivity
- Potential for email/SMS phishing scams
QR Code
How it Works: A QR code is generated by the MDM system, which the end-user or admin scans to begin the enrollment process.
-
Pros:
- Quick and easy for on-site enrollments
- Reduced error rates compared to manual entry
- Can be printed or displayed for mass enrollments
- Code can carry custom metadata for specific use cases
-
Cons:
- Requires physical presence for scanning
- Potential for QR code tampering if not securely managed
- Can carry confidential information such as network configuration
Manual Entry
How it Works: Admins or end-users manually enter device details and configuration settings into the MDM system.
-
Pros:
- High level of control over individual device configurations
- No need for additional technologies like email or QR scanners
-
Cons:
- Time-consuming
- Prone to human error
- Not scalable for large deployments
Zero Touch (Android) / Automated Device Enrollment (iOS)
How it Works:
-
- Android: Devices are automatically enrolled on the first boot-up or after a factory reset, provided they are pre-configured with Android Zero Touch.
- iOS: Devices purchased through Apple's business or education programs can be automatically enrolled into MDM during the initial setup process with Automated Device Enrollment.
-
Pros:
- Smooth experience for end-users
- High level of control for administrators
- Ideal for large-scale, organization-wide deployments
- Supports advanced configurations and policy enforcement from the get-go
- Locks the device with the managing organization
-
Cons:
- Requires devices to be purchased through specific channels
- Not suitable for BYOD setups
- Initial setup may require more time and coordination between IT and procurement
If you're aiming for top-notch security and scalability, Zero Touch for Android or Automated Device Enrollment for iOS should be your go-to options.
For those seeking the highest level of flexibility, particularly in diverse device environments, QR Code stands out as an excellent choice.
Lastly, if you're operating within a Bring Your Own Device (BYOD) policy framework, Over-the-Air (OTA) or self-registration methods offer an optimal blend of user convenience and administrative control. The key is to align your choice of enrollment method with your organization's specific needs, security requirements, and operational constraints. With versatile MDM solutions like Appaloosa, admins have the flexibility to tailor their enrollment strategies to meet these diverse needs effectively.
Best Practices for Simplified Enrollment
Optimizing the enrollment process is about much more than just saving time; it's also a critical measure for reducing errors and achieving scalability. One of the best practices that IT administrators should employ is batch enrollment for large deployments. This approach allows for the simultaneous enrollment of multiple devices, simplifying the operational aspects and saving valuable time for your IT team.
Before initiating any enrollment, it's imperative to ensure that all pre-requisites are met. This includes checking hardware compatibility, updating to the necessary operating systems, and ensuring that all necessary apps and configurations are ready to be deployed. Failing to meet these prerequisites can result in time-consuming setbacks, complicating the enrollment process and increasing the chances of errors.
A well-documented enrollment workflow should be in place. This workflow serves as a roadmap for the enrollment process, outlining each step clearly and serving as a reference for team members. Proper documentation can significantly reduce the margin for error and offer a scalable method for future deployments.
Another essential consideration is matching the right enrollment method with the right audience. Whether it's Zero Touch for high-security enterprise devices, QR codes for flexible, multi-device environments, or OTA for BYOD scenarios, choosing the most appropriate method can have a significant impact on the success of your Mobile Device Management (MDM) strategy.
By focusing on these best practices, IT admins can create an efficient, error-free, and scalable enrollment process tailored to their specific organizational needs and the diverse user base they serve
Common Pitfalls and How to Avoid Them
Despite the best-laid plans and meticulous preparation, enrollment processes can sometimes run into issues. While these setbacks can be frustrating, understanding common pitfalls can significantly improve an administrator's ability to preempt problems before they escalate into major setbacks.
Network Issues: One of the most common problems during device enrollment is network connectivity issues. Whether it's poor Wi-Fi strength, congested networks, or even complete outages, these problems can bring the enrollment process to a grinding halt. As a preventive measure, IT administrators should perform network assessments prior to the enrollment to ensure that connectivity is stable and solid. It's also advisable to have backup network options in place.
Incorrect Credentials: Typos and human error can result in incorrect credentials being entered, causing unnecessary delays. Ensuring that credentials are double-checked, ideally through a two-step verification process, can minimize this issue. Automating the credential input through batch processing or other automated methods can also help circumvent this common pitfall.
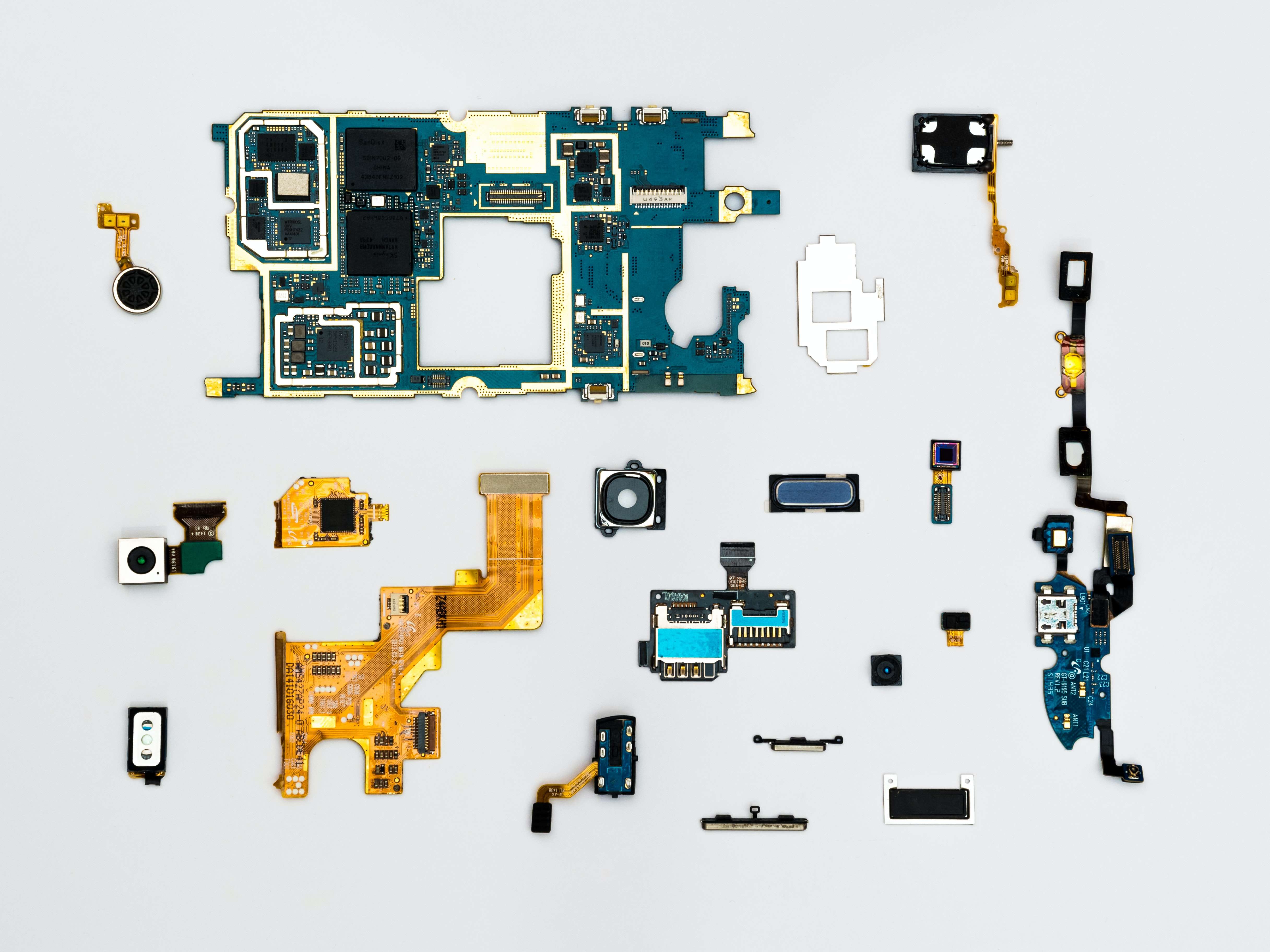
Device Compatibility: Another common issue is hardware or software incompatibility. Before the enrollment process, administrators should verify that the devices being enrolled meet the minimum system requirements for the MDM solution. This entails confirming the device's operating system, processing speed, and other hardware specifications. If overlooked, incompatibilities can create complications that are cumbersome and time-consuming to resolve.
Lack of Documentation: In the absence of a well-documented workflow, the enrollment process can become prone to errors and inefficiencies. Clear guidelines and procedures should be documented and made easily accessible to all team members involved in the enrollment. This not only standardizes the procedure but also serves as a helpful troubleshooting guide when issues arise.
Overlooking User Training: Sometimes, the issue isn't with the technology but with the end-users who may not be familiar with the enrollment procedures. Providing a simple yet complete user guide, or even a short training session for users, can go a long way in avoiding this pitfall.
Ignoring Security Protocols: Skipping or rushing through security measures in a hurry to complete the enrollment can lead to vulnerabilities. Always ensure that security protocols, such as encryption and two-factor authentication, are not only implemented but also rigorously tested.
Thinking Outside the Box: While conventional methods and online guides are valuable, don't overlook the power of in-person interaction. Consider organizing regular enrollment events where IT admins invite and assist users with device onboarding. These physical events can not only speed up the enrollment process but also offer real-time solutions to any issues that may arise. This proactive approach helps in reducing potential blocking issues and can lead to a more simplified enrollment experience for everyone involved.
By proactively identifying and preparing for these common pitfalls, administrators can significantly reduce the likelihood of encountering issues during the enrollment process, leading to a more efficient and smooth-running MDM system.
Device Configuration
Introduction to Device Profiles
Configuring device profiles allows administrators to enforce policies and control various device features remotely. These profiles can manage everything from Wi-Fi settings to screen lock requirements.
How to Set Up Wi-Fi, Email, and VPN Configuration
Network configurations like Wi-Fi, Email, and VPN are commonly controlled through MDM solutions. Detailed steps for setting up these configurations effectively can save admins a lot of troubleshooting time later on.
Importance of Testing Configurations
It's not enough to simply roll out configurations; they must be rigorously tested to ensure they are applied correctly and don't disrupt other functionalities.
Software and App Management
Managing Corporate App Stores
Having a centralized corporate app store simplifies the task of software distribution. Learn how to add, remove, or update applications within this secure framework.
Pushing Updates and Software Patches
Software patches and updates are crucial for device health and security. Knowing when and how to push these updates can make the difference between a secure and a compromised network.
Application Whitelisting and Blacklisting
Controlling which apps can be installed on devices is crucial for data security. App whitelisting is usually the approach for VIP users, whereas BYOD users may have a more flexible list of approved corporate apps along with the ability to download from public app stores, barring a few blacklisted applications.
Role-Based Access Control (RBAC)
Understanding RBAC in an MDM Context
Role-Based Access Control allows admins to fine-tune policies depending on a user's or device's role within the organization. For instance, a BYOD user may require different permissions than a corporate device user.
Implementing Role-Specific Policies
Mapping user roles to device policies is essential for maintaining a secure yet flexible MDM environment. This is particularly useful for distinguishing between user-owned devices and shared devices, like rugged devices or kiosks.
BYOD vs. Corporate vs. Rugged vs. Kiosk Devices
Knowing how to distinguish between these different device types is key for applying the appropriate policies. This enables admins to make the right decisions based on the user or device type, without compromising security or usability.
Remote Wipe and Lock

Situations Warranting Remote Actions
Sometimes, remote actions like wiping a device or locking it are necessary for safeguarding corporate data. Understanding when these actions are warranted can be crucial for minimizing potential risks.
Legal Implications and User Notifications
Before executing a remote wipe or lock, it's important to understand the legal boundaries and the necessity of informing the device's user. This is particularly true in BYOD scenarios, where personal data might also be at stake.
Monitoring and Reporting
Importance of Continuous Monitoring
Regular monitoring is not just for identifying issues but also for preemptive action against potential risks. Learning to use monitoring tools effectively is key to maintaining a healthy MDM environment.
How to Use Dashboards and Alerts
Most MDM solutions offer dashboards and alerts to make monitoring easier. Knowing how to set these up can make the difference in promptly identifying and responding to issues.
Monthly or Quarterly Reporting Best Practices
Long-term MDM health requires periodic reports to assess the effectiveness of your strategies. This section will offer best practices for what to include in these reports.
Troubleshooting
Common MDM Issues and How to Fix Them
No MDM solution is perfect, and issues can arise. Knowing the common problems and their solutions can save admins a lot of time and headaches.
When to Escalate Issues
Understanding when an issue is beyond basic troubleshooting and needs to be escalated can be crucial for resolving it efficiently.
Importance of Keeping Documentation
Maintaining a solid documentation strategy is essential for long-term MDM success. This helps not only in troubleshooting but also in auditing and compliance.
Compliance and Auditing
Introduction to MDM-Related Compliance Standards
Various regulations, like GDPR, require specific compliance standards. Knowing these is key for avoiding legal ramifications.
Audit Trails and Why They Matter
Audit trails provide a documented history of changes and actions within your MDM solution. These are crucial for compliance and offer a way to backtrack in case of errors or security incidents.
Best Practices for Auditing
Conducting regular audits ensures your MDM solution remains compliant and effective. This section will offer a checklist for what to cover in these audits.
Conclusion
Administering an MDM solution requires a lot of actions, from enrollment to compliance audits. While most MDM solutions on the market require extensive training, Appaloosa.io distinguishes itself by providing an excellent user experience for both admins and users. Appaloosa includes admin training as part of its onboarding process. This enables administrators to fully maintain the platform on their own, without needing to rely on third-party services or spending an excessive amount of time on management tasks. Contact our team to discuss how we can improve your MDM operations.